Communicate securely
In one of our previous articles, various communication protocols were discussed and the process was discussed to make the right choice. One aspect that has not been addressed here is how your data can be safely transferred to the cloud and stored securely in the cloud.
Although this is not important for every product, with a standalone device or a product with an open protocol, there are often no requirements in this area. However, the general trend for products is that they can be provided with new firmware in one way or another. So a connection to the internet is important.
Secure Sockets Layer
A security protocol called SSL (Secure Sockets Layer) was developed in 1994 for the safe transfer of data. Several versions of this security protocol have been released but are now considered unsafe. A successor to SSL is TLS (Transport Layer Security).
 Transport Layer Security
Transport Layer Security
The advantage of TLS is that it is independent of the application protocol and ensures that the data cannot be intercepted or falsified. Several versions of TLS have already been published to be resistant to cyber attacks. Certificates are used to authenticate the data and guarantee privacy. Each certificate has a public key and the owner of the certificate has a private key.
 Privacy
Privacy
To prevent misuse of data, the privacy of data has been laid down in one European privacy law, the General Data Protection Regulation (GDPR) in the Netherlands known as the General Data Protection Regulation (AVG). The law consists of 99 articles ranging from Encryption, Privacy by Design to Disclosure Obligations. Below are two aspects which we explain in more detail.
Encryption
The privacy law does not specify which protocol (for example TLS 1.3) should be used. It is clearly stated that the likelihood of occurrence and the risk must be taken into account, as well as the state of the art and implementation costs. Implementation of the encryption is therefore a piece of custom work and depends on your product and business case.
Privacy by design
The idea behind this is that data protection processes are best adhered to when they are technically integrated during development. The structured approach of a project within Betronic ensures that at the start of a project, the aspects of GDPR . We make a choice of possible solutions together with the customer. The chosen solutions are implemented during the development process.
 Prakticle example
Prakticle example
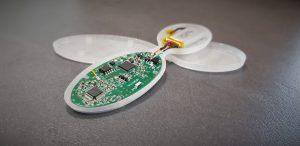
The practical example of this newsletter is the project developed in collaboration with students from TU Delft, the HvA and our own engineers.
This is a product that measures the trend of vital signals from the human body and passes it on to a back office. The trend of the signals is analyzed by an algorithm. With the aid of the analysis, the healthcare authority assesses whether or not action should be taken. An action can consist of scheduling an appointment with a doctor or, for example, a visit by a nurse. The topics of safe communication and privacy are an important ingredient in this product.
Communicate securely
The communication between the sensor for measuring the vital signals and the gateway for sending the data to the back office takes place by means of Bluetooth Low Energy (BLE). BLE is standard equipped with a 128 bit AES-CCM key for data encryption and connection integrity. TLS 1.3 encryption has been chosen for the communication from the gateway to the back office.
Privacy
The user’s information such as name, address and age are not recorded in the sensor or gateway. In the back office, the connection is established between the data from the sensor and the relevant data of the patient. The data is protected by means of user levels with log-in and passwords so that only the right persons can access this data.




